Blog

Five tips to avoiding ransomware
- March 7, 2018
A recent blog post reviewed what Ransomware is, how it is deployed,...

Minding the IT skills gap
- February 28, 2018
The curvature at the edge of a London Underground platform, and the...
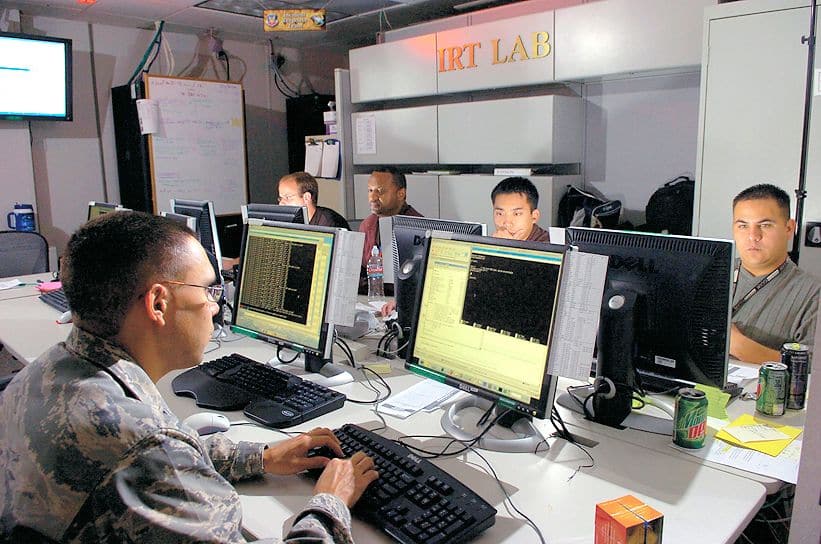
Breaking down what incident response means for your business
- February 21, 2018
In today’s world, Cyber-attacks are becoming the norm – no business or...

Ransomware, what is it?
- February 8, 2018
In today’s world, Cyber-attacks are becoming much more covert and sophisticated in...

The cybersecurity analyst certification
- January 30, 2018
One of the hottest certs in Information Technology is the Cybersecurity Analyst,...

Business cybersecurity: Take a lesson from Custer’s last stand
- January 24, 2018
On June 25, 1876, Lt. Col. George Armstrong Custer started into a...