Self-Paced Learning: Why It’s the Future of IT Education
The digital age has revolutionized countless aspects of our lives, and education is no exception. With advancements in technology, the way we learn has undergone a transformation, especially in fields like IT. Traditional classroom setups, while valuable, can sometimes feel restrictive—fixed schedules, fast-paced lectures, and standardized approaches may not suit every learner’s style or needs. Enter self-paced learning: a flexible, tailored educational model that’s rapidly gaining traction in IT education.
With more than 65% of students reporting that they prefer self-paced online courses over traditional classes, the demand for flexible learning options is only increasing. Here’s a closer look at why self-paced learning is quickly becoming the go-to choice for aspiring IT professionals and why it could be the future of IT education.
What is Self-Paced Learning?
Self-paced learning is a format where students have the flexibility to start and progress through a course at their own speed. It allows learners to adapt their schedules, revisit challenging material, or accelerate through familiar topics without being tethered to a strict timeline. Instead of following a fixed syllabus or pace, self-paced courses put students in control of their learning journey.
Benefits of Self-Paced Learning in IT Education
Self-paced learning offers unique advantages that are particularly well-suited to the fast-evolving IT industry. Here are some of the core benefits:
- Flexibility to Fit Diverse Schedules
- Self-paced courses allow learners to study at their own convenience, making it possible for professionals to balance learning with work, personal life, and other commitments. This flexibility is especially valuable for those working in demanding IT roles or those balancing full-time jobs while upskilling.
- Enhanced Retention and Comprehension
- Learners can spend more time on complex concepts or labs until they feel fully confident. By learning at a comfortable pace, students often achieve better retention and a deeper understanding of technical material, which is essential in IT roles where foundational skills are critical.
- Revisiting Content as Needed
- IT can be a complex field, with evolving technologies and nuanced concepts. Self-paced learners can pause, rewind, and revisit content whenever needed, helping them solidify knowledge without feeling rushed.
- Cost-Effectiveness
- Self-paced courses often come at a lower cost than traditional classes. Additionally, the flexibility can save learners money on commuting, relocation, or other associated expenses of in-person education.
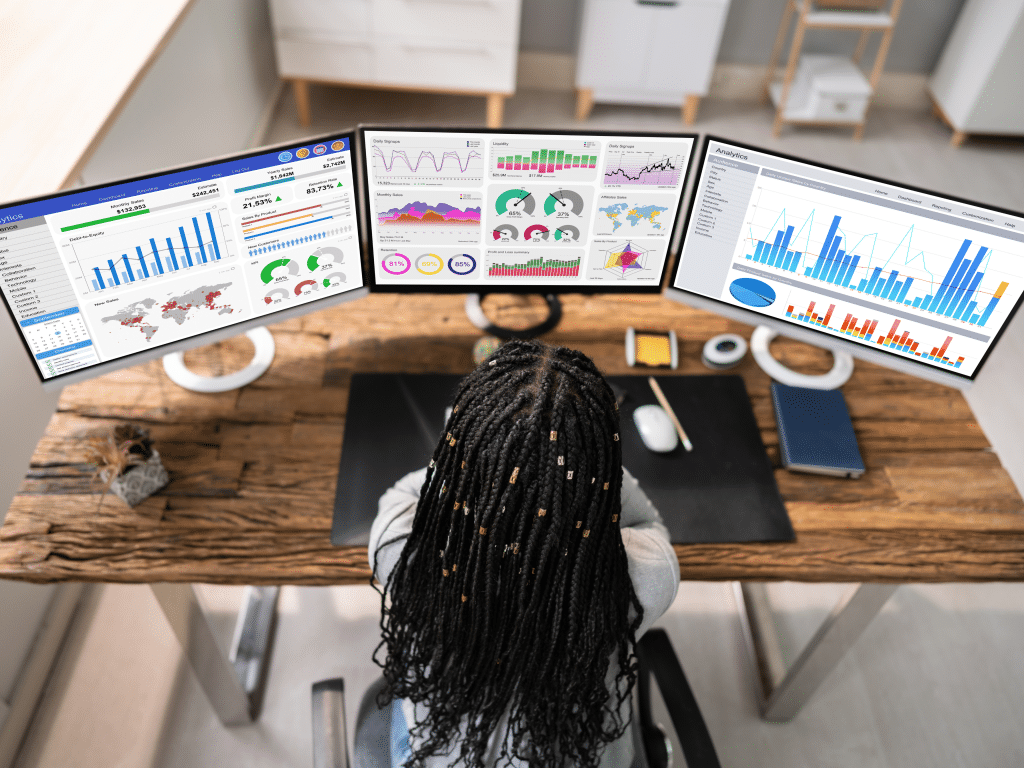
- Practical Experience with Virtual Labs and Simulations
- Many self-paced IT courses incorporate hands-on learning experiences such as virtual labs, enabling students to apply theoretical knowledge in a simulated environment. This is critical for IT, where practical skills like coding, network configuration, and cybersecurity measures are essential.

Why Self-Paced Learning is the Future of IT Education
In the rapidly changing world of IT, where new technologies emerge frequently, keeping up requires adaptable, forward-thinking educational approaches. Self-paced learning aligns perfectly with these demands:
- Quick Adaptation to New Technologies: As technology advances, IT professionals can take courses on specific skills or tools without waiting for the next semester or year. They can jump right into a new certification course or module, adapting to industry changes at their own pace.
- Lifetime Learning Mindset: Self-paced learning fosters a culture of ongoing education. IT professionals can continue to build skills, take on new roles, and pursue additional certifications without interrupting their careers.
Skills Best Suited for Self-Paced Learning in IT
Certain skills and certifications in IT lend themselves particularly well to the self-paced format:
- Networking Fundamentals: Courses like CompTIA Network+ allow students to grasp core networking principles at their own pace, applying them as they gain experience.
- Cybersecurity Skills: In areas like penetration testing or cybersecurity fundamentals, self-paced learning offers the ability to revisit complex labs and simulations.
- Cloud Computing: Skills like those required for AWS or Azure certifications can be acquired step-by-step, making it easy for learners to dive into specialized modules as needed.
Final Note on Self-Paced Learning in IT Education
With its flexibility, accessibility, and learner-centered approach, self-paced learning is reshaping IT education. It empowers students to learn at their own speed, revisit challenging material, and develop the in-depth skills necessary for today’s IT roles. Embracing self-paced education could well be the key to building a highly-skilled, adaptable IT workforce for the future.
This is where Ascend Education comes in. With our virtual labs, simulations, and a variety of self-paced courses, we’re dedicated to supporting learners on their journey to mastering critical IT skills. Whether you’re a beginner or an experienced professional, Ascend’s resources can help you stay current and competitive in an evolving industry.